Valid 70-697 Dumps shared by PassLeader for Helping Passing 70-697 Exam! PassLeader now offer the newest 70-697 VCE dumps and 70-697 PDF dumps, the PassLeader 70-697 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-697 dumps with VCE and PDF here: http://www.passleader.com/70-697.html (201 Q&As Dumps –> 308 Q&As Dumps –> 350 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-697 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpd0pjaGx0bzVXVG8
QUESTION 46
You have a computer named Computer1 that runs Windows 10 Enterprise. You plan to install the most recent updates to Computer1. You need to ensure that you can revert to the current state of Computer1 in the event that the computer becomes unresponsive after the update. What should you include in your solution?
A. The Reset this PC option from the Recovery section of the Settings app
B. The Sync your settings options from the Accounts section of the Settings app
C. The Backup and Restore (Windows 7) control panel item
D. The Refresh your PC option from the PC Settings
Answer: C
Explanation:
The question states that you need to ensure that you can revert to the current state of Computer1. The question does not specify what exactly the current state is in terms of software configuration but it would be safe to assume that Computer1 has Windows Store Apps installed, desktop applications installed and some previous Windows Updates installed. The only way to recover the computer to its `current’ state is to perform a full backup of the computer before updating it. Then if the computer becomes unresponsive after the update, we can simply restore the backup to return the computer to its state at the time of the backup.
Incorrect Answers:
A: When you Reset your PC, all your applications and data will be removed. It is like doing a complete Windows reinstall and formatting your hard drive.
B: The Sync your settings options are used for syncing settings with a Microsoft account. This does not return the computer to its current state.
D: When you Refresh your PC, your data, Windows Store Apps and application settings will be preserved. However, all your desktops applications and any existing Windows Updates will be removed. This does not return the computer to its current state.
http://www.howtogeek.com/220986/how-to-use-all-of-windows-10%E2%80%99s-backup-and-recovery-tools/
QUESTION 47
You administer a Windows 10 Enterprise computer. The computer has File History turned on, and system protection turned on for drive C. You accidentally delete a folder named Libraries\Customers by using the Shift+Delete keyboard shortcut. You need to restore the most recent version of the folder to its original location. Which approach should you use to restore the folder?
A. Recycle Bin
B. the latest restore point
C. File History
D. a manually selected restore point
Answer: C
Explanation:
File History is similar to Previous Versions in previous versions of Windows. It takes regular backups of your data and saves them to a separate disk volume or external drive. When File History is enabled, it backs up all the system libraries and your custom libraries by default. To restore a deleted folder, you can browse to the parent folder or library and select Restore Previous Versions. The Previous Versions tab will list the previous versions that can be restored to its original location or restored to an alternative location.
Incorrect Answers:
A: The question states that you deleted the folder by using the Shift+Delete keyboard shortcut. The Shift +Delete keyboard shortcut bypasses the Recycle Bin; the file or folder is permanently deleted without moving it to the Recycle Bin.
B: System Restore points do not back up user data. They are used for restoring the system and applications to a previous state. You cannot use a System Restore point to recover a deleted folder.
D: System Restore points do not back up user data. They are used for restoring the system and applications to a previous state. You cannot use a System Restore point to recover a deleted folder.
https://www.winhelp.us/file-history-in-windows-8.html
QUESTION 48
Hotspot Question
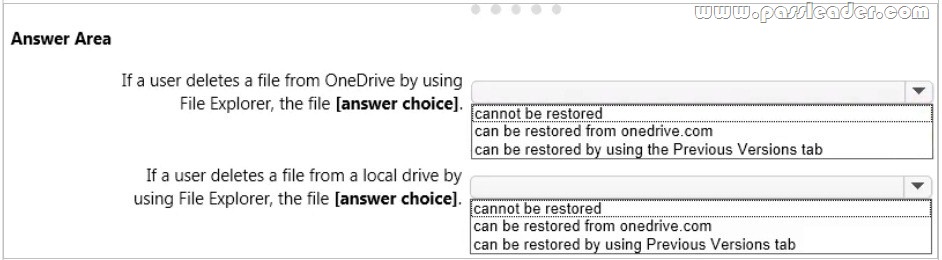
You have a standalone computer that runs Windows 10 Enterprise. The computer is configured to automatically back up files by using File History. The user of the computer uses the OneDrive desktop app to sync files. The Previous Versions settings from the local group policy of the computer are shown in the following graphic.
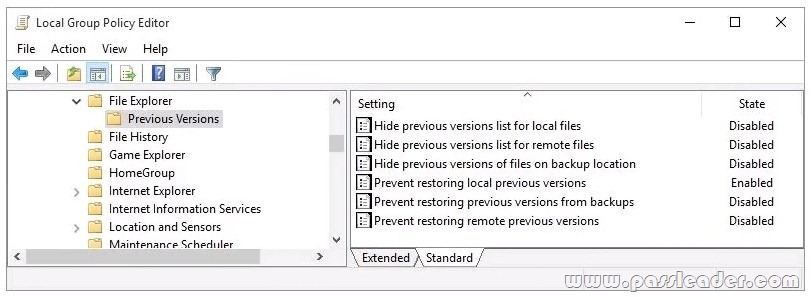
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic. NOTE: Each correct selection is worth one point.
Answer:

Explanation:
When a file is deleted from the local OneDrive folder with File Explorer, the deletion is replicated to Onedrive.com and the file is moved to the OneDrive recycle bin. The deleted file can therefore be recovered from the Recycle Bin on Onedrive.com. If a user deletes a file from a local drive by using File Explorer, the file cannot be restored. If the file is not in the OneDrive folder, it will not be a file that is synced to onedrive.com. We could use Previous Versions to restore the file but this is prevented by the Group Policy settings. The “Prevent restoring local previous versions”-Enabled group policy setting would prevent the previous version from being restored.
http://www.groovypost.com/howto/restore-deleted-files-local-onedrive-folder/
QUESTION 49
You have a Windows 10 Enterprise computer named Computer1. Computer1 has File History enabled. You create a folder named Folder1 in the root of the C: drive. You need to ensure that Folder1 is protected by File History. What are two possible ways to achieve the goal? Each correct answer presents a complete solution.
A. From File Explorer, include Folder1 in an existing library.
B. Modify the Advanced settings from the File History Control Panel item.
C. From the Settings app, modify the Backup options.
D. From File Explorer, modify the system attribute of Folder1.
Answer: AC
Explanation:
By default, File History backs up all libraries. We can therefore ensure that Folder1 is protected by File History by adding the folder to a library. The second method of ensuring that Folder1 is protected by File History is to add the folder location to File History. You do this by modifying the Backup options, not the File History Control Panel item as you might expect. In the Settings app, select Update & Security then Backup. Under the Back up using File History heading, select the Add a drive option.
Incorrect Answers:
B: The Advanced settings from the File History Control Panel item are for configuring settings such as backup frequency, the size of the offline cache and the amount of time that previous versions should be kept for. This is not where you can configure Folder1 to be protected by File History.
D: You cannot configure Folder1 to be protected by File History by modifying the system attribute of the folder. System files are not automatically protected by File History.
https://www.winhelp.us/file-history-in-windows-8.html
QUESTION 50
A company has 100 client computers that run Windows 10 Enterprise. A new company policy requires that all client computers have static IPv6 addresses. You need to assign static IPv6 addresses to the client computers. Which Network Shell (netsh) command should you run?
A. add address
B. set interface
C. set global
D. set address
Answer: A
Explanation:
The add address Network Shell (netsh) command adds an IPv6 address to a specified interface.
Incorrect Answers:
B: The set interface Network Shell (netsh) command modifies interface configuration parameters.
C: The set global Network Shell (netsh) command modifies global configuration parameters.
D: The set address Network Shell (netsh) command modifies an IPv6 address on a specified interface.
https://technet.microsoft.com/en-gb/library/cc740203(v=ws.10).aspx#BKMK_3
QUESTION 51
Hotspot Question
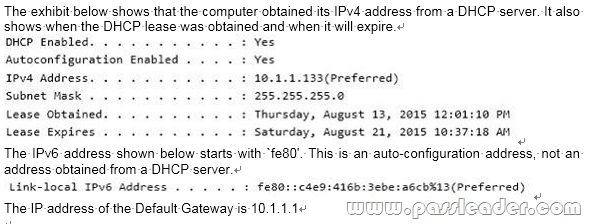
You have a network that contains Window 10 Enterprise computers. The network configuration of one of the computers is shown in the following output.
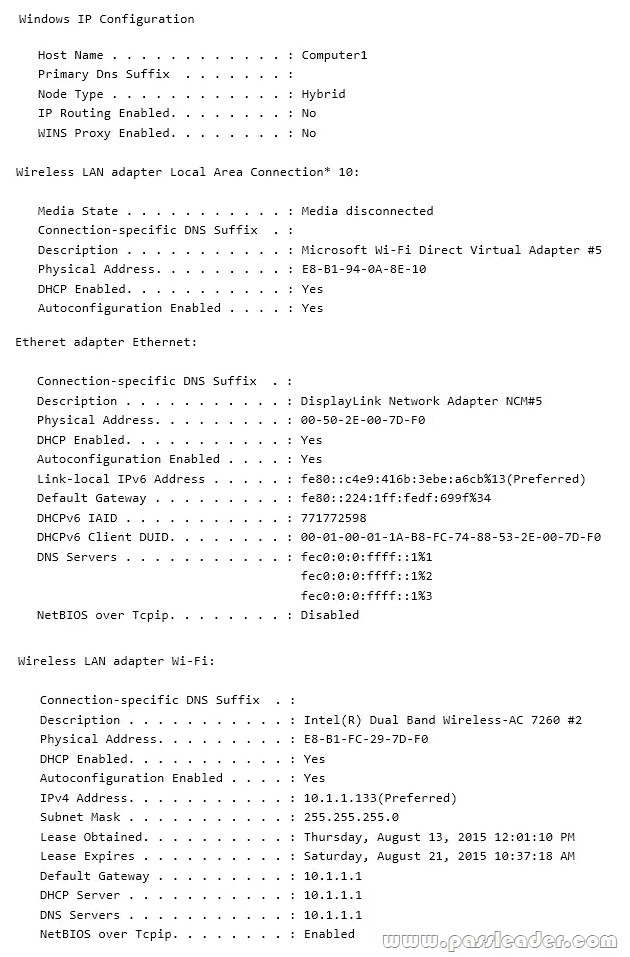
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the output. NOTE: Each correct selection is worth one point.

QUESTION 52
Hotspot Question
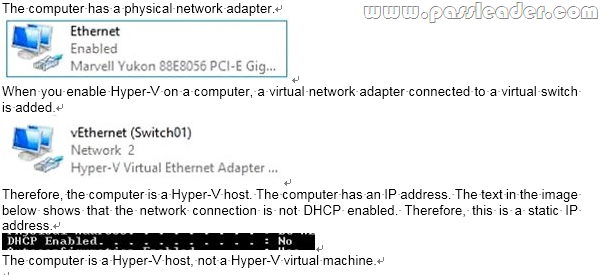
You are setting up a Windows 10 Enterprise computer. The computer’s network connections are shown in the Network connections exhibit. (Click the Exhibit button.)

The computer’s network settings are shown in the Network Settings exhibit. (Click the Exhibit button.)

Advanced TCP/IP settings are shown in the Advanced TCP/IP Settings exhibit. (Click the Exhibit button.)

For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.

QUESTION 53
A company has client computers that run Windows 10. The client computer systems frequently use IPSec tunnels to securely transmit data. You need to configure the IPSec tunnels to use 256-bit encryption keys. Which encryption type should you use?
A. 3DES
B. DES
C. RSA
D. AES
Answer: D
Explanation:
IPSec tunnels can be encrypted by 256-bit AES. L2TP/IPsec allows multiprotocol traffic to be encrypted and then sent over any medium that supports point-to-point datagram delivery, such as IP or Asynchronous Transfer Mode (ATM). The L2TP message is encrypted with one of the following protocols by using encryption keys generated from the IKE negotiation process: Advanced Encryption Standard (AES) 256, AES 192, AES 128, and 3DES encryption algorithms.
QUESTION 54
You administer a group of 10 client computers that run Windows 10. The client computers are members of a local workgroup. Employees log on to the client computers by using their Microsoft accounts. The company plans to use Windows BitLocker Drive Encryption. You need to back up the BitLocker recovery key. Which two options can you use? (Each correct answer presents a complete solution. Choose two.)
A. Save the recovery key to a file on the BitLocker-encrypted drive.
B. Save the recovery key in the Credential Store.
C. Save the recovery key to SkyDrive.
D. Print the recovery key.
Answer: CD
Explanation:
It’s not possible to save a Bitlocker file into the same disk. Moreover, what would be the point to save recovery key on the drive, which is locked and you cannot access it without the key anyway.
QUESTION 55
You are using sysprep to prepare a system for imaging. You want to reset the security ID (SID) and clear the event logs. Which option should you use?
A. /generalize
B. /oobe
C. /audit
D. /unattend
Answer: A
Explanation:
Generalize prepares the Windows installation to be imaged. If this option is specified, all unique system information is removed from the Windows installation. The security ID (SID) resets, any system restore points are cleared, and event logs are deleted. The next time the computer starts, the specialize configuration pass runs. A new security ID (SID) is created, and the clock for Windows activation resets, if the clock has not already been reset three times.
QUESTION 56
Group Policy is a set of rules which control the working environment of user accounts and computer accounts. Group Policy provides the centralized management and configuration of operating systems, applications and users’ settings in an Active Directory environment. In other words, Group Policy in part controls what users can and can’t do on a computer system. Which one of these policies requires a reboot?
A. Turn off Windows Defender
B. Turn off Autoplay for non-volume devices
C. Disable Active Desktop
D. Turn off Data Execution Prevention for Explorer
Answer: D
Explanation:
You can Turn Off Windows Defender anytime (Uninstalling it is another thing!) without rebooting. A reboot is REQUIRED when turning off DEP for Explorer.
QUESTION 57
Which term is used to refer to installing apps directly to a device without going through the Windows Store?
A. SQL Injection
B. BranchCache
C. DLL Hijack
D. Sideloading
Answer: D
QUESTION 58
IPv6 has a vastly larger address space than IPv4. This expansion provides flexibility in allocating addresses and routing traffic and eliminates the primary need for network address translation (NAT). Do you know how many more bits there are in an IPv4 address compared to an IPv6 address?
A. 4 times more
B. 6 times more
C. Twice as many
D. 8 times more
Answer: A
Explanation:
IPv4 addresses are 32 bit, IPv6 addresses are 128 bit.
QUESTION 59
You are using sysprep to prepare a system for imaging. You want to enable end users to customize their Windows operating system, create user accounts, name the computer, and other tasks. Which sysprep setting should you use?
A. /oobe
B. /audit
C. /generalize
D. /unattend
Answer: A
Explanation:
The /oobe option restarts the computer into Windows Welcome mode. Windows Welcome enables end users to customize their Windows operating system, create user accounts, name the computer, and other tasks. Any settings in the /oobe System configuration pass in an answer file are processed immediately before Windows Welcome starts.
QUESTION 60
You have set up a new wireless network for one of your prestigious clients. The director wants to ensure that only certain designated wireless laptops can connect to the new network to prevent misuse. What do you need to do?
A. Use MAC address control
B. Use IPv4 address control
C. Use WEP
D. Use WPA
Answer: A
Explanation:
Media Access Control address (MAC address) is a unique identifier assigned to most network adapters or network interface cards (NICs) by the manufacturer for identification, and used in the Media Access Control protocol sub-layer. If assigned by the manufacturer, a MAC address usually encodes the manufacturer’s registered identification number. It may also be known as an Ethernet Hardware Address (EHA), hardware address, adapter address, or physical address.
Get the newest PassLeader 70-697 VCE dumps here: http://www.passleader.com/70-697.html (201 Q&As Dumps –> 308 Q&As Dumps –> 350 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-697 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpd0pjaGx0bzVXVG8