Valid 70-410 Dumps shared by PassLeader for Helping Passing 70-410 Exam! PassLeader now offer the newest 70-410 VCE dumps and 70-410 PDF dumps, the PassLeader 70-410 exam questions have been updated and ANSWERS have been corrected, get the newest PassLeader 70-410 dumps with VCE and PDF here: http://www.passleader.com/70-410.html (512 Q&As Dumps –> 528 Q&As Dumps)
BTW, DOWNLOAD part of PassLeader 70-410 dumps from Cloud Storage: https://drive.google.com/open?id=0B-ob6L_QjGLpfnJzOE1fWnlJOWVtaE93SnJNT3gtaTNYYnVpZkw5THBSMWRKbFlfaXh1azg
QUESTION 81
Your network contains an Active Directory domain named contoso.com. All domain controllers run Windows Server 2012 R2. The domain contains a server named Server1 that runs Windows Server 2012 R2. You need to ensure that when users log on to Server1, their user account is added automatically to a local group named Group1 during the log on process. Which Group Policy settings should you modify?
A. Restricted Groups
B. Security Options
C. User Rights Assignment
D. Preferences
Answer: D
Explanation:
A. If a Restricted Groups policy is defined and Group Policy is refreshed, any current member not on the Restricted Groups policy members list is removed
B. Security settings incorporated into policies are rules that administrators configure on a computer or multiple computers for the purpose of protecting resources on a computer
C. User Rights Assignment policies determines which users or groups have logon rights or privileges on the computer
D. With Preferences, local and domain accounts can be added to a local group without affecting the existing members of the group
http://technet.microsoft.com/en-us/library/cc785631(v=ws.10).aspx
http://www.grouppolicy.biz/2010/01/how-to-use-group-policy-preferences-to-secure-localadministrator-groups/
http://technet.microsoft.com/en-us/library/cc780182(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/hh831424.aspx
QUESTION 82
Your network contains an Active Directory domain named contoso.com. You need to prevent users from installing a Windows Store app named App1. What should you create?
A. An application control policy executable rule
B. An application control policy packaged app rule
C. A software restriction policy certificate rule
D. An application control policy Windows Installer rule
Answer: B
Explanation:
A. For .exe or .com
B. A publisher rule for a Packaged app is based on publisher, name and version
C. You can create a certificate rule that identifies software and then allows or does not allow the software torun, depending on the security level
D. For .msi or .msp
http://technet.microsoft.com/en-us/library/dd759068.aspx
http://technet.microsoft.com/en-us/library/hh994588.aspx
http://www.grouppolicy.biz/2012/08/how-manage-published-a-k-a-metro-apps-in-windows8-using-grouppolicy/
http://technet.microsoft.com/en-us/library/hh994597.aspx#BKMK_Cert_Rules
QUESTION 83
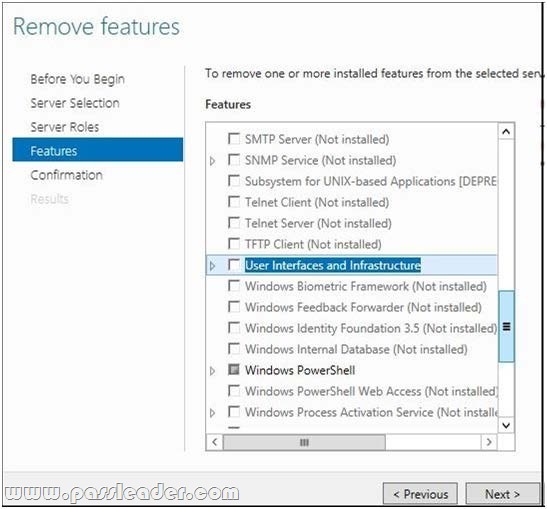
Your company’s security policy states that all of the servers deployed to a branch office must not have the graphical user interface (GUI) installed. In a branch office, a support technician installs a server with a GUI installation of Windows Server 2012 on a new server, and then configures the server as a DHCP server. You need to ensure that the new server meets the security policy. You want to achieve this goal by using the minimum amount of Administrative effort. What should you do?
A. Reinstall Windows Server 2012 on the server.
B. From Windows PowerShell, run Uninstall-WindowsFeature Desktop-Experience.
C. From Windows PowerShell, run Uninstall-WindowsFeature PowerShell-ISE.
D. From Server Manager, uninstall the User Interfaces and Infrastructure feature.
Answer: D
Explanation:
A. Not least effort
B. Uninstalls desktop experience not the full GUI
C. Uninstalls the powershell ISE
D. Least effort and removes full GUI
http://www.howtogeek.com/111967/how-to-turn-the-gui-off-and-on-in-windows-server-2012/
http://technet.microsoft.com/en-us/library/cc772567.aspx
http://blogs.technet.com/b/server_core/archive/2012/05/09/configuring-the-minimal-serverinterface.aspx
QUESTION 84
Your network contains an Active Directory domain named contoso.com. The domain contains 500 servers that run Windows Server 2012 R2. You have a written security policy that states the following:
– Only required ports must be open on the servers.
– All of the servers must have Windows Firewall enabled.
– Client computers used by Administrators must be allowed to access all of the ports on all of the servers.
– Client computers used by the Administrators must be authenticated before the client computers can access the servers.
You have a client computer named Computer1 that runs Windows 8. You need to ensure that you can use Computer1 to access all of the ports on all of the servers successfully. The solution must adhere to the security policy. Which three actions should you perform? (Each correct answer presents part of the solution. Choose three.)
A. On Computer1, create a connection security rule
B. On all of the servers, create an outbound rule and select the Allow the connection if it is secureoption
C. On all of the servers, create an inbound rule and select the Allow the connection if it is secureoption
D. On Computer1, create an inbound rule and select the Allow the connection if it is secureoption
E. On Computer1, create an outbound rule and select the Allow the connection if it is secureoption
F. On all of the servers, create a connection security rule
Answer: ACF
Explanation:
http://technet.microsoft.com/en-us/library/cc772017.aspx
Unlike firewall rules, which operate unilaterally, connection security rules require that both communicating computers have a policy with connection security rules or another compatible IPsec policy.
http://technet.microsoft.com/en-us/library/cc753463.aspx
Traffic that matches a firewall rule that uses the Allow connection if it is secure setting bypasses Windows Firewall. The rule can filter the traffic by IP address, port, or protocol. This method is supported on Windows Vista or Windows Server 2008.
QUESTION 85
Drag and Drop Question
Your network contains three servers. The servers are configured as shown in the following table.
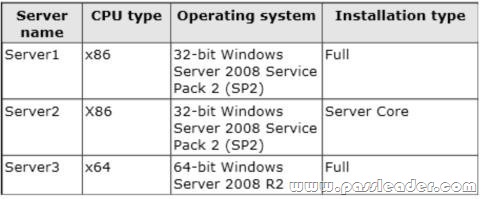
Your company plans to standardize all of the servers on Windows Server 2012 R2. You need to recommend an upgrade path for each server. The solution must meet the following requirements:
– Upgrade the existing operating system whenever possible.
– Minimize hardware purchases.
Which upgrade path should you recommend for each server? To answer, drag the appropriate upgrade path to each server in the answer area. Each upgrade path may be used once, more than once, or not at all.

Answer:
Explanation:
Server1 not 64-bit processor.
Server2 not 64-bit processor.
Server3 64-bit processor, needs 2008 SP1.

http://blogs.technet.com/b/askcore/archive/2012/10/23/upgrading-to-windows-server-2012-part-1.aspx
http://technet.microsoft.com/en-us/library/jj134246.aspx
QUESTION 86
Your network contains a file server named Server1 that runs Windows Server 2012 R2. All client computers run Windows 8. Server1 contains a folder named Folder1. Folder1 contains the installation files for the company’s desktop applications. A network technician shares Folder1 as Share1. You need to ensure that the share for Folder1 is not visible when users browse the network. What should you do?
A. From the properties of Folder1, deny the List Folder Contents permission for the Everyone group.
B. From the properties of Folder1, remove Share1, and then share Folder1 as Share1$.
C. From the properties of Folder1, configure the hidden attribute.
D. From the properties of Share1, configure access-based enumeration.
Answer: B
Explanation:
A. Will deny everyone list of folder content
B. Remove share and re-add using $ for Hidden/Administrative share
C. This will hide the physical folder
D. lists only the files and folders to which they have access when browsing content on the file server
A hidden share is identified by a dollar sign ($) at the end of the share name. Hidden shares are not listed when you look through the shares on a computer or use the “net view” command.
Why Use Hidden Shares?
Using hidden shares on your network is useful if you do not want a shared folder or drive on the network to beeasily accessible. Hidden shares can add another layer of protection for shared files against unauthorizedpeople connecting to your network. Using hidden shares helps eliminate the chance for people to guess yourpassword (or be logged into an authorized Windows account) and then receive access to the shared resource.

http://support.microsoft.com/kb/314984
http://technet.microsoft.com/en-us/library/cc784710(v=ws.10).aspx
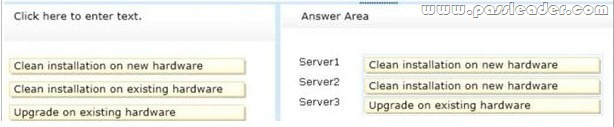
QUESTION 87
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2 and a server named Server2 that runs Windows Server 2008 R2 Service Pack 1 (SP1). Both servers are member servers. On Server2, you install all of the software required to ensure that Server2 can be managed remotely from Server Manager. You need to ensure that you can manage Server2 from Server1 by using Server Manager. Which two tasks should you perform on Server2? (Each correct answer presents part of the solution. Choose two.)
A. Run the systempropertiesremote.execommand
B. Run the Enable-PsRemoting cmdlet
C. Run the Enable-PsSessionConfiguration cmdlet
D. Run the Confiqure-SMRemoting.ps1script
E. Run the Set-ExecutionPolicy cmdlet
Answer: DE
Explanation:
To configure Server Manager remote management by using Windows PowerShell On the computer that you want to manage remotely, open a Windows PowerShell session with elevated user rights. To do this, click Start, click All Programs, click Accessories, click Windows PowerShell, right-click the Windows PowerShell shortcut, and then click Run as administrator. In the Windows PowerShell session, type the following, and then press Enter:
Set-ExecutionPolicy -ExecutionPolicyRemoteSigned
Type the following, and then press Enter to enable all required firewall rule exceptions:
Configure-SMRemoting.ps1 -force -enable
http://technet.microsoft.com/en-us/library/dd759202.aspx
A) Run the systempropertiesremote.exe command.
B) Enable-PSRemoting cmdlet configures the computer to receive Windows PowerShell remote commands that are sent by using the WS-Management technology.
C) Enable-PSSessionConfiguration cmdlet enables registered session configurations that have been disabled.
D) Configure-SMRemoting.ps1 -force -enable.
E) Set-ExecutionPolicy -ExecutionPolicyRemoteSigned.
To configure Server Manager remote management by using Windows PowerShell On the computer that you want to manage remotely, open a Windows PowerShell session with elevated userrights, type the following:
To configure Server Manager remote management by using Windows PowerShell. On the computer that youwant to manage remotely, open a Windows PowerShell session with elevated user rights. To do this, click Start, click All Programs, click Accessories, click Windows PowerShell, right-click the WindowsPowerShell shortcut, and then click Run as administrator. In the Windows PowerShell session, type thefollowing, and then press Enter:
Set-ExecutionPolicy -ExecutionPolicyRemoteSigned
Type the following, and then press Enter to enable allrequired firewall rule exceptions:
Configure-SMRemoting.ps1 -force -enable
http://technet.microsoft.com/en-us/library/dd759202.aspx
QUESTION 88
Hotspot Question
Your network contains an Active Directory domain named contoso.com. The domain contains a print server named Server1 that runs Windows Server 2012 R2. You share several printers on Server1. You need to ensure that you can view the printer objects associated to Server1 in Active Directory Users and Computers. Which option should you select? To answer, select the appropriate option in the answer area.
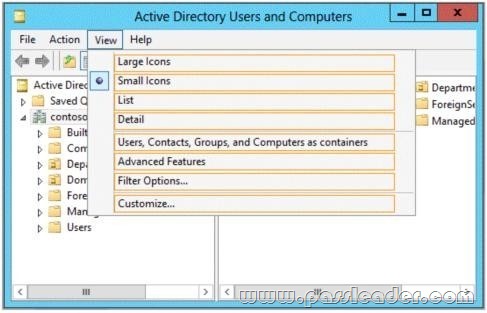
Answer:

Explanation:
You can view printer objects in Active Directory by clicking Users, Groups, and Computers as containers from the View menu in the Active Directory Users and Computers snap-in. By default, printer objects are created under the machine object in which they are shared. After you turn on the Users, Groups, and Computers as containers option, you can see printers by expanding the printer’s host computer.
http://support.microsoft.com/kb/235925
QUESTION 89
Your network contains an Active Directory domain named contoso.com. The domain contains two member servers named Server1 and Server2 that run Windows Server 2012 R2. You log on to Server1. You need to retrieve the IP configurations of Server2. Which command should you run from Server1?
A. winrs -r:server2 ipconfig
B. winrm get server2
C. dsquery *-scope base-attr ip, server2
D. ipconfig > server2.ip
Answer: A
Explanation:
A. Windows Remote Management allows you to manage and execute programs remotely
B. winrm is the server side services for remote mgmt
C. dsquery * finds any objects in the directory according to criteria using a LDAP query
D. Would output server1 ipconfig info to server2.ip file
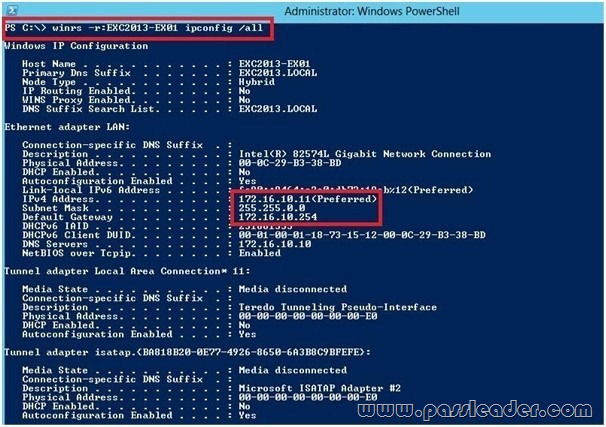
http://technet.microsoft.com/en-us/library/dd349801(v=ws.10).aspx
QUESTION 90
You work as an administrator at contoso.com. The contoso.com network consists of a single domain named contoso.com. All servers on the contoso.com network have Windows Server 2008 R2 installed. Some of contoso.com’s workstations have Windows 7 installed, while the rest have Windows 8 installed. After installing a new Windows Server 2012 computer in the contoso.com domain, you configure it to run the File and Storage Services server role. You are instructed to create a shared folder on the new server, and configure the use of Previous Versions for restoring files located in the shared folder. Which of the following actions should you take?
A. You should consider configuring the Shadow Copies settings on the new server.
B. You should consider configuring the Snapshot settings on the new server.
C. You should consider configuring the Background Copy settings on the new server.
D. You should consider configuring the Permission settings on the new server.
Answer: A
Explanation:
What are previous versions?
Previous versions are either backup copies (copies of files and folders that you back up by using the Back Up Files wizard, or shadow copies) copies of files and folders that Windows automatically saves as part of a restore point. (Shadow copies can be copies of files on your computer or shared files on acomputer on a network.) You can use previous versions of files to restore files that you accidentally modified or deleted, or that were damaged. Depending on the type of file or folder, you can open, save to a different location, or restore a previous version.
ATT: (nothing to do with question but cool to know) File Server Volume Copy Shadow Service (VSS) Agent Service Enables consistency of application snaphots (shadow copies). With previous versions of Windows Server, VSS only supported shadow copies of data on the local server. With WS2012, Microsoft has added VSS for SMB File Shares which extends shadow copy support for network volumes.Administrators install the FS VSS Agent on the file server where the application data is located. They then install the VSS provider in the server where the application is located. The provider talks to the agent using the new File Server Remote VSS protocol in order to manage the shadow copies of the data.
QUESTION 91
You have a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. The disks on Server1 are configured as shown in the exhibit. You create a virtual machine on Server1. You need to ensure that you can configure a pass-through disk for the virtual machine. What should you do?
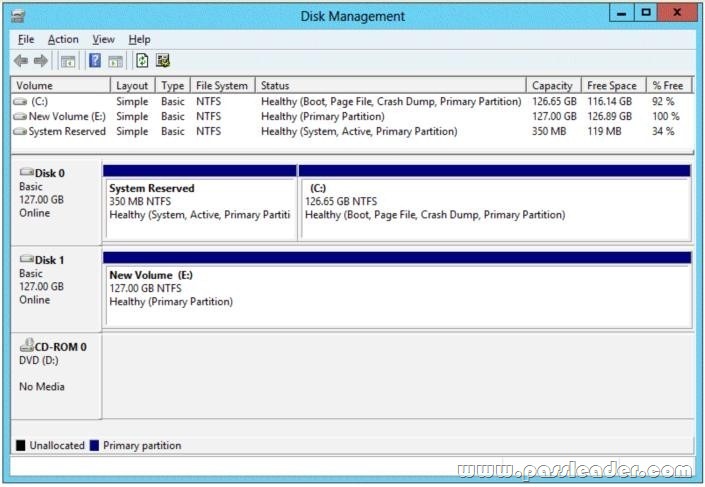
A. Delete partition E
B. Convert Disk 1 to a GPT disk
C. Convert Disk 1 to a dynamic disk
D. Take Disk 1 offline
Answer: D
Explanation:
Pass-Through Disk must be offline.
Pass-through Disk Configuration
Hyper-V allows virtual machines to access storage mapped directly to the Hyper-V server without requiring the volume be configured. The storage can either be a physical disk internal to the Hyper-V server or it can be a Storage Area Network (SAN) Logical Unit (LUN) mapped to the Hyper-V server. To ensure the Guest has exclusive access to the storage, it must be placed in an Offline state from the Hyper-V server perspective.
http://blogs.technet.com/b/askcore/archive/2008/10/24/configuring-pass-through-disks-in-hyper-v.aspx
http://technet.microsoft.com/pt-pt/library/ff404147%28v=ws.10%29.aspx
QUESTION 92
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server2 runs Windows Server 2012 R2. You create a security template named Template 1 by using the Security Templates snap-in. You need to apply template 1 to Server2. Which tool should you use?
A. Security Templates.
B. Computer Management.
C. Security Configuration and Analysis.
D. System Configuration.
Answer: C
Explanation:
Security templates are inactive until imported into a Group Policy Object or the Security Configurationand Analysis.

http://technet.microsoft.com/en-us/library/jj730960.aspx
http://windows.microsoft.com/en-us/windows-vista/using-system-configuration
QUESTION 93
Your network contains an Active Directory domain named contoso.com. The domain contains a domain controller named DCS. DC5 has a Server Core Installation of Windows Server 2012 R2. You need to uninstall Active Directory from DC5 manually. Which tool should you use?
A. The ntdsutil.exe command
B. The dcpromo.exe command
C. The Remove-WindowsFeature cmdlet
D. The Remove-ADComputer cmdlet
Answer: A
Explanation:
The correct Powershell cmdlet would be Uninstall-AddsDomainController.
https://technet.microsoft.com/en-us/library/jj574104.aspx#BKMK_PS
However, since that is not an option, you are left with ntdsutil. Also, the question states that it must be done “manually”, and ntdsutil is a very manual tool.
QUESTION 94
You have a server named Server 2 that runs Windows Server 2012 R2. Server 2 has the Hyper-V server role installed. The disks on Server2 are configured as shown in the exhibit. You create a virtual machine on Server2 named VM1. You need to ensure that you can configure a pass-through disk for VM1. What should you do?
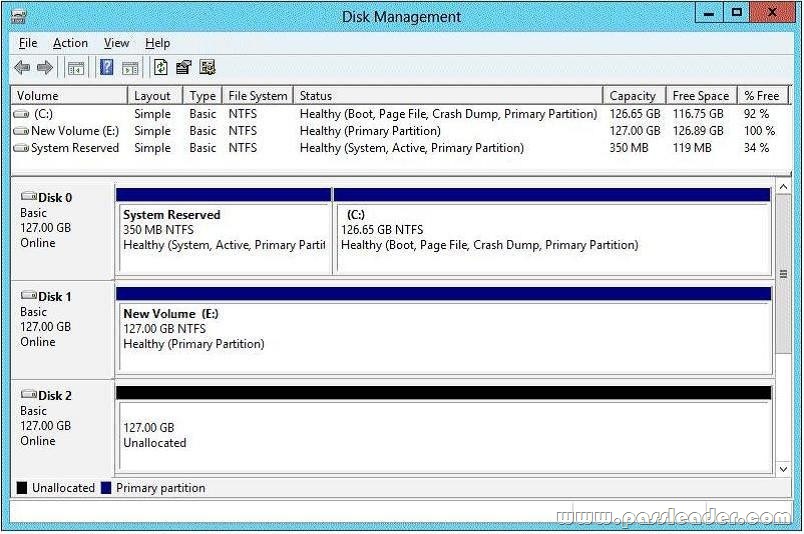
A. Convert Disk 1 to a MBR disk.
B. Convert Disk 1 to a basic disk.
C. Take Disk 1 offline.
D. Create a partition on Disk 1.
Answer: C
Explanation:
Pass-through Disk Configuration
Hyper-V allows virtual machines to access storage mapped directly to the Hyper-V server without requiring the volume be configured. The storage can either be a physical disk internal to the Hyper-V server or it can be a Storage Area Network (SAN) Logical Unit (LUN) mapped to the Hyper-V server. To ensure the Guest has exclusive access to the storage, it must be placed in an Offline state from the Hyper-V server perspective.
http://blogs.technet.com/b/askcore/archive/2008/10/24/configuring-pass-through-disks-in-hyper-v.aspx
QUESTION 95
You have a file server named Server1 that runs Windows Server 2012 R2. Server1 has following hardware configurations:
– 16GB of RAM
– A single quad-core CPU
– Three network teams that have two network adapters each
You add additional CPUs and RAM to Server 1. You repurpose Server1 as a virtualization host. You install the Hyper-V server role on Server1. You need to create four external virtual switches in Hyper-V. Which cmdlet should you run first?
A. Set-NetAdapter
B. Add-Net1.bfoTeamNic
C. Add-VMNetworkAdapter
D. Remove-NetLbfoTeam
Answer: D
Explanation:
A. Sets adapter properties
B. Add new interface to NIC Team
C. Adds vadapter to vm
D. Removed NIC from host
You need 4 virtual switches but currently only have 3 teams available. You would need to break a team first.
http://technet.microsoft.com/en-us/library/jj130875(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/jj130850(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/hh848564(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/jj130848(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/jj130848.aspx
QUESTION 96
Your network contains an Active Directory domain named contoso.com. The domain contains two servers named Server1 and Server2 that run Windows Server 2012 R2. You create a security template named Template1 by using the Security Templates snap-in. You need to apply Template1 to Server2. Which tool should you use?
A. Authorization Manager
B. Local Security Policy
C. Certificate Templates
D. System Configuration
Answer: B
Explanation:
A security policy is a combination of security settings that affect the security on a computer. You can use your local security policy to edit account policies and local policies on your local computer.
QUESTION 97
Your network contains an Active Directory domain named adatum.com. The domain contains a member server named Server1 and a domain controller named DC2. All servers run Windows Server 2012 R2. On DC2, you open Server Manager and you add Server1 as another server to manage. From Server Manager on DC2, you right-click Server1 as shown in the exhibit. You need to ensure that when you right-click Server1, you see the option to run the DHCP console. What should you do?

A. On Server1, install the Feature Administration Tools.
B. In the domain, add DC1 to the DHCP Administrators group.
C. On DC2 and Server1, run winrm quickconfig.
D. On DC2, install the Role Administration Tools.
Answer: D
Explanation:
http://technet.microsoft.com/en-us/library/hh831825.aspx
QUESTION 98
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server 2012. You create a group Manged Service Account named gservice1. You need to configure a service named Service1 to run as the gservice1 account. How should you configure Service1?
A. From a command prompt, run sc.exe and specify the config parameter
B. From Windows PowerShell, run Set-Service and specify the -PassThrough parameter
C. From Windows PowerShell, run Set-Service and specify the -StartupType parameter
D. From Services Console configure the General settings
Answer: A
QUESTION 99
Your network contains an Active Directory domain named contoso.com. An organizational unit (OU) named OU1 contains user accounts and computer accounts. A Group Policy Object (GPO) named GP1 is linked to the domain. GP1 contains Computer Configuration settings and User Configuration settings. You need to prevent the User Configuration settings in GP1 from being applied to users. The solution must ensure that the Computer Configuration settings in GP1 are applied to all client computers. What should you configure?
A. the Group Policy loopback processing mode
B. the Block Inheritance feature
C. the Enforced setting
D. the GPO Status
Answer: A
Explanation:
A. Group Policy loopback with replace option needs to be used
B. Blocking inheritance prevents Group Policy Objects (GPOs) that are linked to higher sites, domains, ororganizational units from being automatically inherited by the child-level
C. Enforced prevent blocking at lower level
D. The GPO Status. This indicates whether either the user configuration or computer configuration of the GPOis enabled or disabled
You can use the Group Policy loopback feature to Apply Group Policy Objects (GPOs) that depend only on which computer the user logs on to. User Group Policy loopback processing can be enabled in one of two modes: merge or replace.
– In merge mode, both GPOs Applying to the user account and GPOs Applying to the computer account are processed when a user logs in. GPOs that Apply to the computer account are processed second and therefore take precedence – if a setting is defined in both the GPO(s) Applying to the user account, and the GPO(s) Applying to the computer account, the setting in the GPO(s) Applying to the computer account will be enforced.
– With the replace mode, GPOs Applying to the user account are not processed only the GPOs Applying to the computer account are Applied. Loopback can be set to Not Configured, Enabled, or Disabled. In the Enabled state, loopback can be set toMerge or Replace. In either case the user only receives user-related policy settings.
* Loopback with Replace — In the case of Loopback with Replace, the GPO list for the user is replaced in its entirety by the GPO list that is already obtained for the computer at computer startup (during step 2 in GroupPolicy processing and precedence). The User Configuration settings from this list are Applied to the user.
* Loopback with Merge — In the case of Loopback with Merge, the Group Policy Object list is a concatenation. The default list of GPOs for the user object is obtained, as normal, but then the list of GPOs for the computer (obtained during computer startup) is appended to this list. Because the computer’s GPOs are processed afterthe user’s GPOs, they have precedence if any of the settings conflict.
You want to create a new OU in AD that is dedicated to computer accounts that will have loopbackprocessing enabled. Create a new GPO in your new OU to enable User Group Policy Loopback Processing and set theappropriate mode (merge/replace). You will define the user settings you want to Apply to the loopback-enabled PCs via GPOs in this same new OU. You can define these settings either in the same GPO where you enabled the User Group Policy Loopback Processing setting, or you create another new GPO in the same OU for your user settings. Remember that when using the REPLACE mode, none of your other user GPOs will be Applied whena user logs in to a machine that has loopback processing enabled. ONLY the user settings that are defined in the GPOs that Apply to that machine will be Applied.
http://msmvps.com/blogs/cgross/archive/2009/10/12/group-policy-loopbackprocessing.aspx
http://technet.microsoft.com/en-us/library/cc782810(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/cc731076.aspx
http://technet.microsoft.com/en-us/library/cc753909.aspx
http://technet.microsoft.com/en-us/library/cc778238%28v=ws.10%29.aspx
http://technet.microsoft.com/en-us/magazine/dd673616.aspx
QUESTION 100
Your network contains two Hyper-V hosts named Host1 and Host2. Host1 contains a virtual machine named VM1. Host2 contains a virtual machine named VM2. VM1 and VM2 run Windows Server 2012 R2. You install the Network Load Balancing feature on VM1 and VM2. You need to ensure that the virtual machines are configured to support Network Load Balancing (NLB). Which virtual machine settings should you configure on VM1 and VM2?
A. Router guard
B. DHCP guard
C. Port mirroring
D. MAC address
Answer: D
Explanation:
In Hyper-V, the VM host prevents dynamic MAC address updates as an extra layer of security in thedatacenter. This is because the VM may have full administrator rights, yet it may be untrusted in thedatacenter, for example when the VM hosting is provided by an independent hosting company. In this scenario,we need to make sure that one VM cannot cause a DOS or information disclosure attack against another VM. If a VM is able to spoof its MAC address, then it can spoof the MAC addresses of other VMs and impactother VMs on that host. The physical switches have similar protections and it is up to the admin to enable thatprotection or not. If you do not enable spoofing of MAC address prior to configuring NLB on the VM you could potentially haveproblems with the NLB cluster. When configuring NLB in unicast mode on Hyper-V with enable spoofing of MAC Address disabled you may see some of the following symptoms:
– When initially configuring NLB you will lose network connectivity on the network adaptor NLB was configured on.
– There will be an NLB error event in the Windows Event Log stating that the network adaptor does not support dynamic MAC address updates.
– After rebooting the server, NLB will appear to be bound to the network adapter, but the cluster VIP will not have been added to the network adaptor.
– The cluster MAC address will still be the original MAC address associated with the network adaptor prior toconfiguring NLB. Use CMD>ipconfig /all to view the MAC address. It should start with “02-BF-***”.
If you ignore all previous symptoms and manually add the VIP you could get an IP conflict if there are other nodes in the cluster that have the same VIP. With that said, to allow VM guests to run NLB you need to set the VM property for “Enable spoofing of MAC Address”. To enable spoofing of MAC Addresses open the Hyper-V management console. Make sure the VM is stopped open the properties of the VM. Select the Network Adaptor for the NLB VM and check the “Enable spoofing of MAC Address” and click OK. Then start the VM.
QUESTION 101
Your network contains a Windows Server 2012 R2 image named Server12.wim. Server12.wim contains the images shown in the following table.
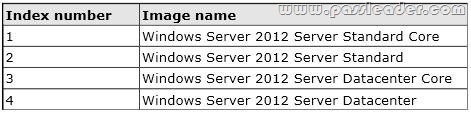
Server12.wim is located in C:\. You need to enable the Windows Server Migration Tools feature in the Windows Server 2012 R2 Server Datacenter image. You want to achieve this goal by using the minimum amount of Administrative effort. Which command should you run first?
A. dism.exe /mount-wim /wimfile:c:\Server12.wim /index:4 /mountdir:c:\mount
B. imagex.exe /capture c: c:\Server12.wim “windows server 2012server datacenter”
C. dism.exe /image: c:\Server12.wim /enable-feature /featurename: servermigration
D. imagex.exe /apply c:\Server12.wim 4 c:\
Answer: A
Explanation:
A. Mounts the image before making any chnages
B. imagex /capture creates windows images .wim
C. You need to mount the image first
D. imagex /Apply Applies image to drive
The Deployment Image Servicing and Management (DISM) tool is a command-line tool that is used to modify Windows images. You can use DISM to enable or disable Windows features directly from the command prompt, or by Applying an answer file to the image. You can enable or disable Windows features offline on a WIM or VHD file, or online on a running operating system. You can also use the DISM image management command to list the image index numbers or to verify the architecture for the image that you are mounting.
http://technet.microsoft.com/en-us/library/hh824822.aspx
http://technet.microsoft.com/en-us/library/hh825258.aspx
http://technet.microsoft.com/en-us/library/cc749447(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/dd744382(v=ws.10).aspx
QUESTION 102
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1. Server1 runs Windows Server 2012 R2 and has the Hyper-V server role installed. On Server1, you create a virtual machine named VM1. When you try to add a RemoteFX 3D Video Adapter to VM1, you discover that the option is unavailable as shown in the following exhibit.

You need to add the RemoteFX 3D Video Adapter to VM1. What should you do first?
A. On Server1, run the Enable-VMRemoteFxPhysicalVideoAdapter cmdlet.
B. On Server1, install the Media Foundation feature.
C. On Server1, run the Add-VMRemoteFx3dVideoAdapter cmdlet.
D. On Server1, install the Remote Desktop Virtualization Host (RD Virtualization Host) role service.
Answer: D
Explanation:
A. Enables one or more RemoteFX physical video adapters for use with RemoteFX-enabled virtual machines
C. Adds a RemoteFX video adapter in a virtual machine
D. Role must be added for host first
http://technet.microsoft.com/en-us/library/hh848506(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/hh848520(v=wps.620).aspx
http://technet.microsoft.com/en-us/library/ff817586(v=ws.10).aspx
QUESTION 103
Your network contains an Active Directory domain named contoso.com. The network contains a domain controller named DC1 that has the DNS Server server role installed. DC1 has a standard primary DNS zone for contoso.com. You need to ensure that only client computers in the contoso.com domain will be able to add their records to the contoso.com zone. What should you do first?
A. Modify the Security settings of DC1
B. Modify the Security settings of the contoso.com zone
C. Store the contoso.com zone in Active Directory
D. Sign the contoso.com zone
Answer: C
Explanation:
C. Only Authenticated users can create records when zone is stored in AD Secure dynamic updates allow an administrator to control what computers update what names and prevent unauthorized computers from overwriting existing names in DNS. If you have an Active Directory infrastructure, you can only use Active Directory – integrated zones on ActiveDirectory domain controllers. If you are using Active Directory – integrated zones, you must decide whether or not to store Active Directory – integrated zones in the Application directory partition. To configure computers to update DNS data more securely, store DNS zones in Active Directory DomainServices (AD DS) and use the secure dynamic update feature. Secure dynamic update restricts DNS zone updates to only those computers that are authenticated and joined to the Active Directory domain where the DNS server is located and to the specific security settings that are defined in the access control lists (ACLs) for the DNS zone.
http://technet.microsoft.com/en-us/library/cc731204(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/cc755193.aspx
http://technet.microsoft.com/en-us/library/cc786068%28v=ws.10%29.aspx
QUESTION 104
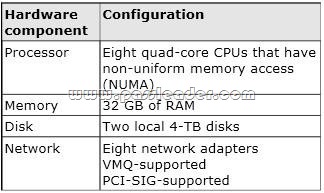
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 hosts four virtual machines named VM1, VM2, VM3, and VM4. Server1 is configured as shown in the following table.

You install a network monitoring application on VM2. You need to ensure that all of the traffic sent to VM3 can be captured on VM2. What should you configure?
A. NUMA topology
B. Resource control
C. Resource metering
D. virtual Machine Chimney
E. the VLAN ID
F. Processor Compatibility
G. the startup order
H. Automatic Start Action
I. Integration Services
J. Port mirroring
K. Single-root I/O virtualization
Answer: J
Explanation:
J. With Hyper-V Virtual Switch port mirroring, you can select the switch ports that are monitored as well as the switch port that receives copies of all the traffic.

http://technet.microsoft.com/en-us/library/jj679878.aspx#bkmk_portmirror
QUESTION 105
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 hosts four virtual machines named VM1, VM2, VM3, and VM4. Server1 is configured as shown in the following table.
You plan to schedule a complete backup of Server1 by using Windows Server Backup. You need to ensure that the state of VM1 is saved before the backup starts. What should you configure?
A. NUMA topology
B. Resource control
C. Resource metering
D. virtual Machine Chimney
E. the VLAN ID
F. Processor Compatibility
G. the startup order
H. Automatic Start Action
I. Integration Services
J. Port mirroring
K. Single-root I/O virtualization
Answer: I
Explanation:
What is the Hyper-V Saved State?
Some Hyper-V virtual machines briefly go offline into a “Saved State” at the initial phase of a backup.
While the backup is running, they usually come back online after a couple of seconds.
Background Knowledge
The decision to pull Hyper-V virtual machines offline into a Saved State is done solely within Hyper-V Management Services. Backup software utilities have no way to force a live backup when Hyper-V determines it can’t and shouldn’t be done.There are many factors that are considered by Hyper-V when it decides whether to take a VM offline or not.
Hyper-V Live Backup Requirements
To achieve zero down time live backups of virtual machines, you need the following conditions met:
1. The VM guest needs to have Integration Services installed, enabled, and running (COM+ System Application Service, Distributed Transaction Coordinator Service, and Volume Shadow Copy Service). Also, review the VM settings in Hyper-V, the ‘backup’ option needs to be checked.
2. All disks involved need to be formatted with NTFS, including the disks within the VM.
3. The Volume Shadow Copy Service and related VSS services need to be enabled and running.
4. The shadow copy storage space for each drive must be available to Hyper-V VSS Writer and be located atthe same volume. For instance, the storage space for drive C: needs to be on drive C: itself, and so on. Use the VSSADMIN command from the command line to check the settings. (Use:
vssadmin list shadowstorage /vssadmin resize shadowstorage)
5. Ensure the VMs are partitioned using ‘basic disk’ formatting.
6. At the moment Hyper-V does not support live backup for VMs formatted using dynamic disk partitioning or GPT.
7. Ensure you have at least about 20% free space on each drive involved, such as the drive on the host and the VM’s main system drive.
8. Ensure plenty of un-fragmented RAM is available on the host. If a machine is pulled into Saved State, Hyper-V may not be able to bring the VM back online if it can’t allocate a continuous block of RAM. Note that there may be sufficient total RAM available but not enough to place a single block. You should therefore aim to keep at least 512MB to 1GB of RAM free when all VMs are powered up.

http://msdn.microsoft.com/en-us/library/dd405549(v=vs.85).aspx
http://backupchain.com/Understanding-Saved-State-Hyper-V-Backup.html
QUESTION 106
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 hosts four virtual machines named VM1, VM2, VM3, and VM4. Server1 is configured as shown in the following table.
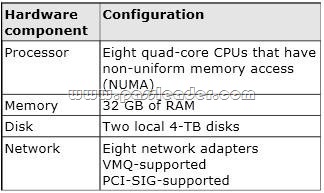
VM3 is used to test applications. You need to prevent VM3 from synchronizing its clock to Server1. What should you configure?
A. NUMA topology
B. Resource control
C. Resource metering
D. virtual Machine Chimney
E. the VLAN ID
F. Processor Compatibility
G. the startup order
H. Automatic Start Action
I. Integration Services
J. Port mirroring
K. Single-root I/O virtualization
Answer: I
Explanation:
By default when you install the Integration Services/Components you get time synchronization with the host OS, here is how to disable on going time synchronization. When you install the integration services/components in Hyper-V virtual machine you get a set of services installed and enabled by default:
– Operating system shutdown
– Time synchronization
– Data exchange heartbeat
– Backup via VSS
If you do not want the virtual machine to continuously synch its time to the Hyper-V host using the integration service, you can disable the integration service from the Hyper-V manager.

http://www.virtualizationadmin.com/kbase/VirtualizationTips/ServerVirtualization/MicrosoftHyper-VTips/PerformanceandScalability/DisablingTimeSyncinaVM.html
http://blogs.technet.com/b/virtualization/archive/2008/08/29/backing-up-hyper-v-virtualmachines.aspx
QUESTION 107
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 hosts four virtual machines named VM1, VM2, VM3, and VM4. Server1 is configured as shown in the following table.

You need to configure VM4 to track the CPU, memory, and network usage. What should you configure?
A. NUMA topology
B. Resource control
C. Resource metering
D. Virtual Machine Chimney
E. the VLAN ID
F. Processor Compatibility
G. the startup order
H. Automatic Start Action
I. Integration Services
J. Port mirroring
K. Single-root I/O virtualization
Answer: C
Explanation:
https://blogs.technet.microsoft.com/meamcs/2012/05/27/hyper-v-resource-metering-in-windows-server-2012-server-8-beta/
Metrics collected for each virtual machine:
– Average CPU usage, measured in megahertz over a period of time.
– Average physical memory usage, measured in megabytes.
– Minimum memory usage (lowest amount of physical memory).
– Maximum memory usage (highest amount of physical memory).
– Maximum amount of disk space allocated to a virtual machine.
– Total incoming network traffic, measured in megabytes, for a virtual network adapter.
– Total outgoing network traffic, measured in megabytes, for a virtual network adapter.
QUESTION 108
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 hosts four virtual machines named VM1, VM2, VM3, and VM4. Server1 is configured as shown in the following table.
You need to ensure that VM1 can use more CPU time than the other virtual machines when the CPUs on Server1 are under a heavy load. What should you configure?
A. NUMA topology
B. Resource control
C. Resource metering
D. Virtual Machine Chimney
E. The VLAN ID
F. Processor Compatibility
G. The startup order
H. Automatic Start Action
I. Integration Services
J. Port mirroring
K. Single-root I/O virtualization
Answer: B
Explanation:
B. Resource controls provide you with several ways to control the way that Hyper-V allocates resources to virtual machine. When you create a virtual machine, you configure the memory and processor to provide the appropriate computing resources for the workload you plan to run on the virtual machine. This workload consists of the guest operating system and all applications and services that will run at the same time on the virtual machine. Resource controls provide you with several ways to control the way that Hyper-V allocates resources to virtual machines.
– Virtual machine reserve. Of the processor resources available to a virtual machine, specifies the percentage that is reserved for the virtual machine. This setting guarantees that the percentage you specify will be available to the virtual machine. This setting can also affect how many virtual machines you can run at one time.
– Virtual machine limit. Of the processor resources available to a virtual machine, specifies the maximum percentage that can be used by the virtual machine. This setting applies regardless of whether other virtual machines are running.
– Relative weight. Specifies how Hyper-V allocates resources to this virtual machine when more than one virtual machine is running and the virtual machines compete for resources.
http://technet.microsoft.com/en-us/library/cc742470.aspx

QUESTION 109
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Hyper-V server role installed. Server1 hosts four virtual machines named VM1, VM2, VM3, and VM4. Server1 is configured as shown in the following table.

VM2 sends and receives large amounts of data over the network. You need to ensure that the network traffic of VM2 bypasses the virtual switches of the parent partition. What should you configure?
A. NUMA topology
B. Resource control
C. Resource metering
D. Virtual Machine Chimney
E. The VLAN ID
F. Processor Compatibility
G. The startup order
H. Automatic Start Action
I. Integration Services
J. Port mirroring
K. Single-root I/O virtualization
Answer: K
Explanation:
K. SR-IOV maximizes network throughput while minimizing network latency as well as the CPU overhead required for processing network traffic.
http://technet.microsoft.com/en-us/library/hh831410.aspx
QUESTION 110
Your network contains an Active Directory domain named contoso.com. The network contains a member server named Server1 that runs Windows Server 2012 R2. Server1 has the DNS Server server role installed and has a primary zone for contoso.com. The Active Directory domain contains 500 client computers. There are an additional 20 computers in a workgroup. You discover that every client computer on the network can add its record to the contoso.com zone. You need to ensure that only the client computers in the Active Directory domain can register records in the contoso.com zone. What should you do first?
A. Move the contoso.com zone to a domain controller that is configured as a DNS server
B. Configure the Dynamic updates settings of the contoso.com zone
C. Sign the contoso.com zone by using DNSSEC
D. Configure the Security settings of the contoso.com zone
Answer: A
Explanation:
If you install DNS server on a non-DC, then you are not able to create AD-integrated zones. DNS update security is available only for zones that are integrated into AD DS. When you directory-integrate a zone, access control list (ACL) editing features are available in DNS Managerso that you can add or remove users or groups from the ACL for a specified zone or resource record.
http://technet.microsoft.com/en-us/library/cc771255.aspx
http://social.technet.microsoft.com/Forums/en-US/winserverNIS/thread/9b041bbc-07654eed-bd1cd65027f05e9f/
http://blogs.msmvps.com/acefekay/2012/11/19/ad-dynamic-dns-updates-registration-rulesof-engagement/
QUESTION 111
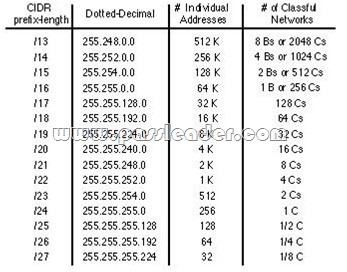
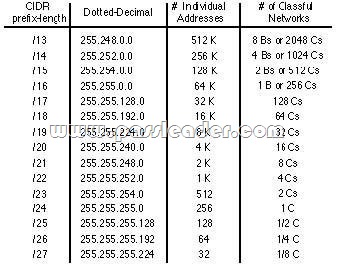
Your company has a remote office that contains 1,600 client computers on a single subnet. You need to select a subnet mask for the network that will support all of the client computers. The solution must minimize the number of unused addresses. Which subnet mask should you select?
A. 255.255.248.0
B. 255.255.252.0
C. 255.255.254.0
D. 255.255.240.0
Answer: A
Explanation:
255.255.252.0 = 11111111.11111111.11111100.00000000 =>( 22 bits 1 … 10 bits 0 ) => 1111111111 = 1023
255.255.254.0 = 11111111.11111111.11111110.00000000 =>( 23 bits 1 … 9 bits 0 ) => 111111111 = 511
255.255.255.0 = 11111111.11111111.11111111.00000000 =>( 24 bits 1 … 8 bits 0 ) => 11111111 = 255
255.255.255.128 = 11111111.11111111.11111111.10000000 =>( 25 bits 1 … 7 bits 0 ) => 1111111 = 127
http://zeus.fh-brandenburg.de/~ihno/doc/lehre/internet/ip_eng.html
QUESTION 112
You plan to deploy a DHCP server that will support four subnets. The subnets will be configured as shown in the following table.

You need to identify which network ID you should use for each subnet. What should you identify? To answer, drag the appropriate network ID to the each subnet in the answer area.

Answer:

Explanation:
http://zeus.fh-brandenburg.de/~ihno/doc/lehre/internet/ip_eng.html
QUESTION 113
You work as a senior administrator at contoso.com. The contoso.com network consists of a single domain named contoso.com. All servers on the contoso.com network have Windows Server 2012 R2 installed, and all workstations have Windows 8 installed. You are running a training exercise for junior administrators. You are currently discussing a Windows PowerShell cmdlet that activates previously de-activated firewall rules. Which of the following is the cmdlet being discussed?
A. Set-NetFirewallRule
B. Enable-NetFirewallRule
C. Set-NetIPsecRule
D. Enable-NetIPsecRule
Answer: B
Explanation:
Enable-NetFirewallRule – Enables a previously disabled firewall rule.
http://technet.microsoft.com/en-us/library/cc990290(v=ws.10).aspx
http://technet.microsoft.com/en-us/library/jj574205.aspx
http://mikefrobbins.com/2013/02/28/use-powershell-to-remotely-enable-firewall-exceptions-on-windows-server-2012/
http://technet.microsoft.com/en-us/library/jj554869%28v=wps.620%29.aspx
QUESTION 114
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 is located on the same subnet as all of the client computers. A network technician reports that he receives a “Request timed out” error message when he attempts to use the ping utility to connect to Server1 from his client computer. The network technician confirms that he can access resources on Server1 from his client computer. You need to configure Windows Firewall with Advanced Security on Server1 to allow the ping utility to connect. Which rule should you enable?
A. File and Printer Sharing (Echo Request – ICMPv4-In)
B. Network Discovery (WSD-In)
C. File and Printer Sharing (NB-Session-In)
D. Network Discovery (SSDP-In)
Answer: A
Explanation:
Ping uses ICMP
Open Control Panel, then select System and Security by clicking on that header Select Windows Firewall, Advanced Settings. In `Windows Firewall with Advanced security’ click on `Inbound rules’. Scroll down to `File and Printer sharing(Echo request ICMPv4-In)’. Right click on the rule and select `Enable rule’.

Make sure that it turns green.

Powershell:
Import-Module NetSecurity
Set-NetFirewallRule -DisplayName “File and Printer Sharing (Echo Request ?ICMPv4-In)”
-enabled True
QUESTION 115
You have a file server named Server1 that runs Windows Server 2012 R2. You need to ensure that a user named User1 can use Windows Server Backup to create a complete backup of Server1. What should you configure?
A. The local groups by using Computer Management
B. A task by using Authorization Manager
C. The User Rights Assignment by using the Local Group Policy Editor
D. The Role Assignment by using Authorization Manager
Answer: A
Explanation:
A. User needs to be added to local Backup Operator group
B. AzMan is a role-based access control (RBAC) framework that provides an administrative tool to manage authorization policy and a runtime that allows Applications to perform access checks against that policy
C. User Rights Assignment policies determines which users or groups have logon rights or privileges on the computer
D. AzMan is a role-based access control (RBAC) framework that provides an administrative tool to manage authorization policy and a runtime that allows Applications to perform access checks against that policy
http://technet.microsoft.com/en-us/library/cc780182(v=ws.10).aspx
http://msdn.microsoft.com/en-us/library/bb897401.aspx
QUESTION 116
Your network contains a production Active Directory forest named contoso.com and a test Active Directory forest named contoso.test. A trust relationship does not exist between the forests. In the contoso.test domain, you create a backup of a Group Policy Object (GPO) named GPO1. You transfer the backup of GPO1 to a domain controller in the contoso.com domain. You need to create a GPO in contoso.com based on the settings of GPO1. You must achieve this goal by using the minimum amount of Administrative effort. What should you do?
A. From Windows PowerShell, run the Get-GPO cmdlet and the Copy- GPO cmdlet.
B. From Windows PowerShell, run the New-GPO cmdlet and the Import- GPO cmdlet.
C. From Group Policy Management, create a new starter GPO. Right-click the new starter GPO, and then click Restore from Backup.
D. From Group Policy Management, right-click the Croup Policy Objects container, and then click Manage Backups.
Answer: B
Explanation:
A. Copy-GPO requires domain trust/copy from one domain to another domain within the same forest
B. The Import-GPO cmdlet imports the settings from a GPO backup into a specified target GPO. The target GPO can be in a different domain or forest than that from which the backup was made and it does not have to exist prior to the operation
D: You can also restore GPOs. This operation takes a backed-up GPO and restores it to the same domain from the GPO’s original which it was backed up. You cannot restore a GPO from backup into a domain different of domain
The New-GPO cmdlet creates a new GPO with a specified name. By default, the newly created GPO is not linked to a site, domain, or organizational unit (OU). The Import-GPO cmdlet imports the settings from a GPO backup into a specified target GPO. The target GPO can be in a different domain or forest than that from which the backup was made and it does not have to exist prior to the operation. The Restore-GPO cmdlet restores a GPO backup to the original domain from which it was saved. If the original domain is not available, or if the GPO no longer exists in the domain, the cmdlet fails.
http://technet.microsoft.com/en-us/library/cc781458(v=WS.10).aspx
http://technet.microsoft.com/en-us/library/hh967461.aspx
http://technet.microsoft.com/en-us/library/ee461050.aspx
http://technet.microsoft.com/en-us/library/ee461044.aspx
http://blogs.technet.com/b/askpfeplat/archive/2012/11/04/windows-server-2012-the-new-and-improved-group-policy-management-console.aspx
QUESTION 117
Your network contains an active directory forest. The forest functional level is Windows Server 2012. The forest contains a single domain. The domain contains a member server named Server1 that run windows server 2012. You purchase a network scanner named Scanner1 that supports Web Services on Devices (WDS). You need to share the network scanner on Server1. Which server role should you install on Server1?
A. Web Server (IIS)
B. Fax Server
C. File and Storage Services
D. Print and Document Services
Answer: D
Explanation:
Print and Document Services enables you to centralize print server and network printer tasks. With this role, you can also receive scanned documents from network scanners and route the documents to a shared network resource, Windows SharePoint Services site, or email addresses. Windows Server 2012 uses Web Services on Devices (WSD) technologies to integrate scanning devices into the system.
http://technet.microsoft.com/en-us/library/hh831468.aspx
http://technet.microsoft.com/en-us/library/jj134196.aspx
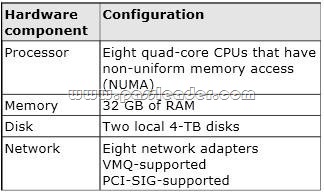
QUESTION 118
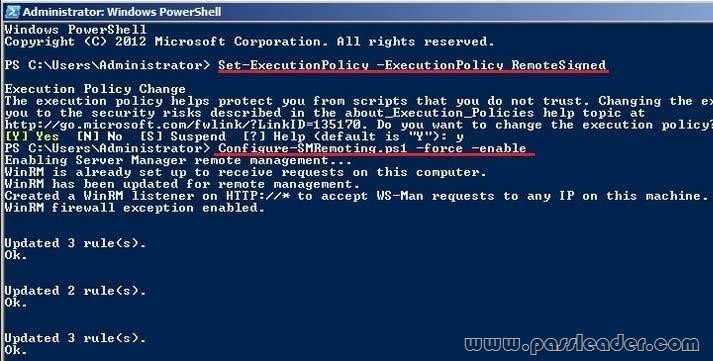
Your network contains an Active Directory forest named adatum.com. The forest contains a child domain named asia.adatum.com. The asia.adatum.com child domain contains a server named DHCP1 that runs Windows Server 2012 R2. You install the DHCP Server server role on DHCP1. You have access to the administrative accounts shown in the following table.

You need to authorize DHCP1. Which user account should you use?
A. Admin1
B. Admin2
C. Admin3
D. Admin4
Answer: B
Explanation:
http://technet.microsoft.com/en-us/library/cc759688(v=ws.10).aspx
QUESTION 119
Your network contains a server named Server1 that runs Windows Server 2012 R2. App1 has the Print and Document Services server role installed. All client computers run Windows 8. The network contains a network-attached print device named Printer1. From App1, you share Printer1. You need to ensure that users who have connected to Printer1 previously can print to Printer1 if App1 fails. What should you configure? To answer, select the appropriate option in the answer area.

Answer:

Explanation:
Branch Office Direct Printing can reduce Wide Area Network (WAN) usage by printing directly to a print device instead of a server print queue. This feature can be enabled or disabled on a per printer basis and is transparent to the user. It is enabled by an administrator using the Print Management Console or Windows PowerShell on the server. The printer information is cached in the branch office, so that if the print server is unavailable for some reason (for example if the WAN link to the data center is down), then it is still possible for the user to print. Branch Office Direct Printing requires the following operating systems:
– Windows Server 2012
– Windows 8
http://technet.microsoft.com/en-us/library/jj134156.aspx
QUESTION 120
You have a server named Server1. Server1 runs Windows Server 2012 R2. Server1 has two network adapters and is located in a perimeter network. You need to install a DHCP Relay Agent on Server1. Which node should you use to add the DHCP Relay Agent? To answer, select the appropriate node in the answer area.
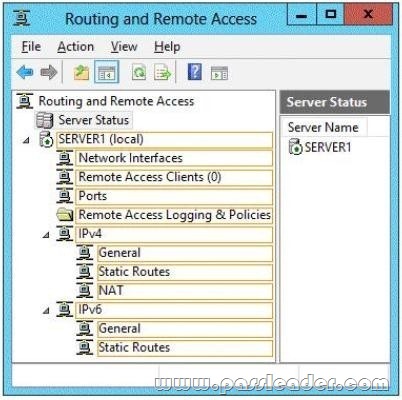
Answer:

Explanation:
Membership in the local Administrators group, or equivalent, is the minimum required to complete this procedure. To configure the IPv4 DHCP relay agent:
1. In the Routing and Remote Access MMC snap-in, expand IPv4, right-click General, and then click New Routing Protocol.
2. In the New Routing Protocol dialog box, select DHCPv4 Relay Agent, and then click OK.
3. In the navigation pane, right-click DHCPv4 Relay Agent, and then click New Interface.
4. Add the network interfaces on which the server might receive DHCPv4 requests that you want to send to the DHCP server. Right-click DHCPv4 Relay Agent, click New Interface, select the appropriate network interface, and then click OK.
5. In the DHCP Relay Properties dialog box, select Relay DHCP packets, and then click OK.
6. In the navigation pane, right-click DHCP Relay Agent, and then click Properties.
7. On the General tab, enter the IPv4 address of the DHCP servers that you want to provide DHCP services for the RRAS server’s clients, click Add, and then click OK.
http://technet.microsoft.com/en-us/library/dd469685.aspx
Get the newest PassLeader 70-410 VCE dumps here: http://www.passleader.com/70-410.html (512 Q&As Dumps –> 528 Q&As Dumps)
And, DOWNLOAD the newest PassLeader 70-410 PDF dumps from Cloud Storage for free: https://drive.google.com/open?id=0B-ob6L_QjGLpfnJzOE1fWnlJOWVtaE93SnJNT3gtaTNYYnVpZkw5THBSMWRKbFlfaXh1azg